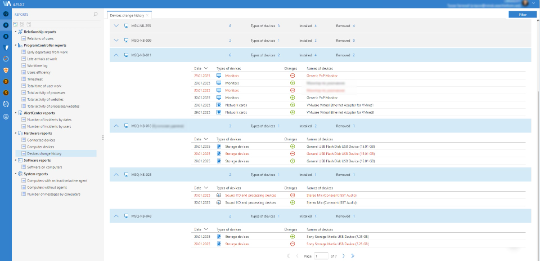
Risk Monitor
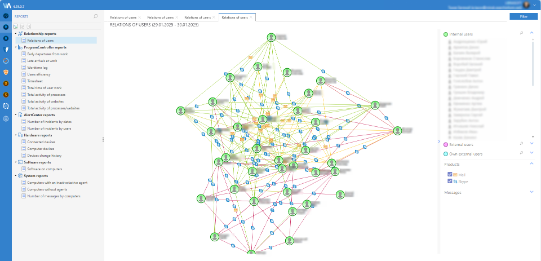
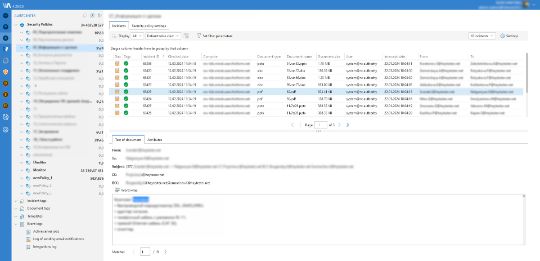
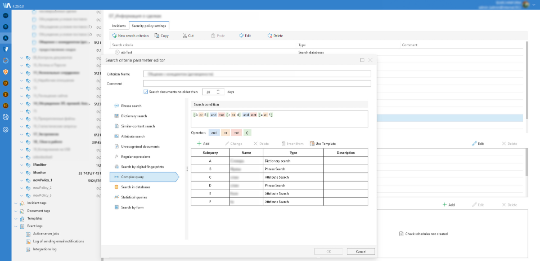
Risk Monitor is a next generation DLP
And even more than DLP
Single agent
comprehensive risk
management platform
FORENSIC SUIT
TIME TRACKING
FILEAUDITOR
Security
Security

SearchInform product was included in Gartner Magic
Quadrant in 2017 and recognized by the Radicati
Group in “Enterprise Data Loss Prevention Market,
2017-2021” research.
Monitor your
employees activities
and keep track of
the data 24/7
Facilitating compliance
-
Solving regulatory compliance issues
-
Conducting forensics and retrospective investigation
User Centric Security
-
Helping to increase staff productivity
-
Assisting team loyalty management
-
Safeguarding the company against personnel risks and predicting employee behavior patterns
-
Controlling the human factor
Data Centric Security
-
Immunization to the consequences of data leakage
-
Taking care for the most sensitive data on corporate devices
SearchInform helps monitor pay-offs and
corruption, provides workplace morale
analysis, detects risk groups, and more.
business: financial services, insurance,
manufacturing, healthcare, retail, etc.
policies cost-free at the client’s request,
which are necessary to comply with the
corporate rules and local law
Benefits

explore more about SearchInform
product modules and their capabilities
in a Module Comparison Table
Explore more

Learn more, how to enhance the protection of
your company with the help of Risk Monitor and
other solutions by SearchInform.
Reviews
Information Services

“With the SearchInform solution, we improved employees' performance by monitoring their daily behaviour. At first, the system seems complicated, but after you start working with it daily, you intuitively understand everything.
The system is transparent to the end user. With two clicks, you can track everything the user did with the information.”
Information Technology and Services

“The SearchInform risk monitoring is an awe-inspiring tool. I have never seen a tool that collects so many data from a computer and organizes it in a way to be clear about what was made in the hosts. It is pretty useful to collect evidence on actions of internal users from conversations, accesses, software that were used, the path from where a data was collected to where it was sent, and even capturing from webcam, microphone and displays.”
Computer & Network Security

“The next-gen DLP - Risk Monitor is such a comprehensive solution that has a function for every department in your business. This solution is the only solution we are familiar with that can reveal the fraud and empower risk managers and C-Level executives to protect organization's digital assets, and increase staff performance while at the same time prevent the wide range of risks.”
Industrial Automation

“SearchInform solutions give all you need to monitor your data, network, and hardware, so you can make necessary enhancements to your information security system and IT infrastructure as a whole.”
Start Your Free 30-day
Trial Now!
SearchInform uses four types of cookies as described below. You can decide which categories of cookies you wish to accept to improve your experience on our website. To learn more about the cookies we use on our site, please read our Cookie Policy.
Necessary Cookies
Always active. These cookies are essential to our website working effectively.
Cookies does not collect personal information. You can disable the cookie files
record
on the Internet Settings tab in your browser.
Functional Cookies
These cookies allow SearchInform to provide enhanced functionality and personalization, such as remembering the language you choose to interact with the website.
Performance Cookies
These cookies enable SearchInform to understand what information is the most valuable to you, so we can improve our services and website.
Third-party Cookies
These cookies are created by other resources to allow our website to embed content from other websites, for example, images, ads, and text.
Please enable Functional Cookies
You have disabled the Functional Cookies.
To complete the form and get in touch with us, you need to enable Functional Cookies.
Otherwise the form cannot be sent to us.

Subscribe to our newsletter and receive a bright and useful tutorial Explaining Information Security in 4 steps!

Subscribe to our newsletter and receive case studies in comics!