Information security in the broadest sense is a combination of means to protect information from accidental or deliberate exposure. The owner of the information bears losses regardless of whether the impact was caused by natural or artificial factors.
Principles of information security
Integrity means the capability of data to keep the original form and structure during storing and after repeated transfers. Only the owner or user with legal access to the data has the right to edit, delete or supplement the information.
Confidentiality reveals the need to restrict access to information resources for a certain circle of people. During actions and operations, information is only accessible to users who are included in the information systems and have been successfully authenticated.
Accessibility means that public information should be made available to authorized users of resources in a timely and unhindered manner.
Authenticity shows that the information belongs to a trusted person or owner who at the same time acts as a source of information.
Provision and sustainment of information security involves a set of various measures to prevent, monitor and eliminate unauthorized third-party access. Information security measures are also aimed at protection from damaging, distorting, blocking or copying information. All tasks should be addressed simultaneously, only then complete and reliable protection is ensured.
Keep corporate data safe with a free trial!
Main questions about the information protection method are especially acute when hacking or theft with distortion of information lead to severe consequences or financial damages.
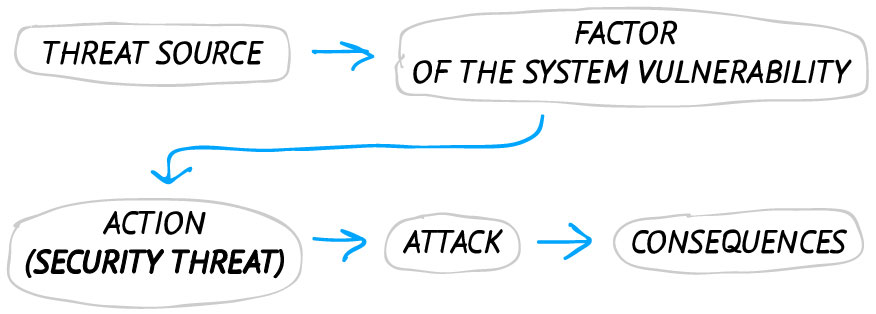
There is the following logical chain of information transformation created with modeling:

Types of information security threats
Information threat is a potentially possible influence or impact on an automated system with the subsequent damage to someone's needs.
To date, there exist more than one hundred positions and types of threats to the information system. It is extremely important to analyze all risks using different diagnostic techniques. Based on the analyzed detailed indicators, you can competently build a system of protection against threats in the information space.
Classification of security vulnerabilities
Information security threats are not manifested independently but through possible contact with the gaps in the protection system, or factors of vulnerability. The threat leads to the disruption in systems on a specific carrier.
The main vulnerabilities are caused by the following factors:
- Shortcomings of software or hardware
- Different characteristics of the structure of automated systems in the information flow
- Some operational processes of the system are inadequate
- Inaccuracy of information exchange protocols and interface
- Difficult operating conditions and conditions in which the information is located.
Most often the sources of threats are triggered in order to obtain illegal benefits after damaging information. However, accidental effect of threats due to insufficient protection and mass attack of a threatening factor is also possible.
Vulnerabilities can be:
- Objective
- Random
- Subjective.
If you eliminate or at least mitigate the impact from vulnerabilities, you can avoid a significant threat meant to damage the storage system.
Random vulnerabilities
These factors vary depending on unforeseen circumstances and features of the information environment. They are almost impossible to predict in the information space, but you have to be prepared to rapidly eliminate them. Engineering and technical investigation or a response attack will help to mitigate the following problems:
1. System failures:
- Caused by malfunctions of technical means at different levels of processing and storage of information (including those responsible for system performance and access to it).
- Malfunctions and obsolete elements (demagnetization of data carriers, such as diskettes, cables, connection lines and microchips).
- Malfunctions of different software that supports all links in the chain of information storage and processing (antiviruses, application and service programs).
- Malfunctions of auxiliary equipment of information systems (power transmission failures).
2. Factors weakening information security:
- Damage to communications such as water supply, electricity, ventilation and sewerage.
- Malfunctions of enclosing devices (fences, walls in buildings, housing of the equipment where information is stored).
Objective vulnerabilities
They depend on the technical design of the equipment which is installed on the object requiring protection, as well as its characteristics. It is impossible to escape all these factors, but their partial elimination can be achieved through engineering techniques in the following cases:
1. Related to emission technical means:
- Electromagnetic techniques (side emission and signals from cable lines, elements of technical means).
- Sound versions (acoustic or with vibration signals).
- Electrical (slip of signals into the circuits of electrical network, through the induction into the lines and conductors, because of uneven current distribution).
2. Activated:
- Malware, illegal programs, technological exits from programs which are together called ‘implant tools’.
- Hardware implants: introduced directly into telephone lines, electrical networks or premises.
3. Due to the characteristics of a protected object:
- Object location (visibility and absence of a controlled zone around the information object, presence of vibration or sound reflecting elements around the object, presence of remote elements of the object).
- Arrangement of information exchange channels (use of radio channels, lease of frequencies or use of shared networks).
4. Those that depend on the characteristics of carriers:
- Parts with electro-acoustic modifications (transformers, telephone devices, microphones and loudspeakers, inductors).
- Elements under the influence of electromagnetic field (carriers, microcircuits and other elements).
Subjective vulnerabilities
In most cases, the vulnerabilities of this subtype result from inadequate employee actions at the level of storage and protection system development. Eliminating such factors is possible using hardware and software:
1. Inaccuracies and gross errors that violate information security:
- At the stage of loading the ready software or preliminary algorithm development, as well as during its use (possibly, during daily use or during data entry).
- When managing programs and information systems (difficulties in the training to work with the system, individual set up of services, manipulation of information flows).
- During the use of technical equipment (during switch-on or switch-off, the use of devices for transmitting or receiving information).
2. System malfunctions in the information environment:
- The mode of protection of personal data (the problem may be caused by laid-off employees or current employees during off-hours when they get unauthorized access to the system).
- Safety and security mode (when accessing facilities or technical devices).
- While working with devices (inefficient energy use or improper equipment maintenance).
- While working with data (change of information, its saving, search and destruction of data, elimination of defects and inaccuracies).


Vulnerability ranking
Specialists should consider and evaluate each vulnerability. Therefore, it is important to determine the criteria for assessing the threat of damage to the protection and the probability of its breakage or bypassing. The indicators are calculated with the use of ranking. There are three main criteria:
- Accessibility is a criterion that takes into account how convenient it is for a threat source to use a particular type of vulnerability to disrupt information security. The indicator includes the technical data of the information carrier (such as equipment dimensions, its complexity and cost, as well as the possibility of using non-specialized systems and devices for hacking information systems).
- Fatality is a characteristic that assesses the vulnerability impact on the ability of programmers to cope with the consequences of the threat for information systems. When assessing only objective vulnerabilities, it is necessary to define their information capacity or the ability to transmit to another place a useful signal with confidential data without deforming it.
- Quantity is a characteristic of counting the parts of information storage and implementation systems which are prone to any vulnerability.
To find out the accurate information about protection level, you need to engage the analytical department. They will evaluate all the vulnerabilities and will make an information map with five point grading scale. The 1 corresponds to the minimal impact on the protection and its bypassing while the 5 corresponds to the maximum impact and, accordingly, the danger. The results are recorded in one table, and the impact level is broken down into categories for convenient calculation of the vulnerability factor.
What sources threaten information security?
Threats bypassing the protection of information security can be divided into several categories. The concept of categories is mandatory, since it simplifies and systematizes all factors without exception. The main parameters are
1. The degree of intentionality of intervention in the information protection system:
- Threats caused by unwitting employees in the information dimension
- Threats triggered by fraudsters for personal gain.
2. Signs of occurrence:
- Artificial information security threat provoked by human hands
- Natural threatening factors beyond the control of information protection systems caused by natural disasters.
3. Classification of the immediate cause of the threat. The perpetrator can be:
- A person who disclose confidential information by bribing company employees.
- A natural factor like a catastrophe or local disaster.
- Software with the use of specialized devices or the introduction of malicious code in technical means which disturbs the functioning of the system.
- Accidental deletion of data, authorized software and hardware funds, failure of the operating system.
4. Severity of threats on information resources:
- At the moment of data processing in the information space (mailings from virus utilities).
- At the time of receiving new information.
- Regardless of the performance of information storage system (in the case of breaking ciphers or cryptographic protection of information).
DETECT INTERNAL SECURITY THREATS
There is another classification of IS threats. It is based on other parameters and is also used during the analysis of the system malfunction or hacking. The following is taken into account:
Threat source status:
- In the system itself, which leads to operational errors and failures when using AS resources.
- Within the AS's visibility, for example, the use of listening equipment, the theft of information in the printed form or the theft of records from data carriers.
- Fraud outside the coverage area of the AS. The information can be captured during the transfer through communication paths, incidental capture from acoustic or electromagnetic emission of devices.
Impact degree:
- An active security threat that changes the structure and nature of the system, for example, the use of malicious viruses or Trojans.
- Passive threat steals information through copying, sometimes being hidden. It does not make changes to the information system.
Damages
Severity and manifestations of a damage can be different:
- Non-pecuniary and pecuniary damages caused to individuals whose information was stolen.
- Financial loss with regard to the expenses incurred on restoring information systems.
- Material costs associated with the inability to perform work because the information security system was changed.
- Reputational damage associated with the brand reputation and resulting in disturbed relations at global level.
The person who committed the offense (received unauthorized access to information, or hacked into the protection system) can cause damage. Damage can also occur regardless of the subject owning information, but because of external factors and impacts (technological and natural disasters). In the first case, the responsibility falls on the subject, the components of the crime are defined, and offenders are punished through judicial proceedings. An act can be committed:
- With a criminal intent (direct or indirect)
- Through negligence (without intentional harm).
The punishment for an offense is chosen according to the current national legislation or according to the criminal code in the first case. If the crime is committed through negligence, and the damage incurred is small, the case will be under civil, administrative or arbitration law.
Sign up for a free trial

Subscribe to our newsletter and receive a bright and useful tutorial Explaining Information Security in 4 steps!

Subscribe to our newsletter and receive case studies in comics!