Сorporate fraud
Corporate fraud often stems from low organizational management level, inadequate risk assessment and disregard for tasks allocation and roles delimitation
Governance, Risk and Compliance (GRC) framework, which addresses these issues and determines key points which must accord with established standards and not affect business continuity, is created on the basis of evaluation of controls’ relevance conducted by all the specialists responsible for internal threat mitigation.
3 lines of defense
Risk Monitor
Identify violations of various types - theft, kickbacks, bribes, etc.
Protect your data and IT infrastructure with advanced auditing and analysis capabilities
Monitor employee productivity, get regular reports on top performers and slackers
Conduct detailed investigations, reconstructing the incident step by step
01
Management
Controls
Code of conduct
The code demands that a specific rule set is abided by. Each department can have its own instruction regarding safety and security. For example, if private devices are restricted in some area or access rights are limited and rigorously managed, the risk of incidents caused by improperly configured access or leakage through personal gadgets can be minimized.
Ethics & compliance
A company’s ethics and compliance management program is designed as a guidance facilitating conformity to the established corporate ethical norms and regulatory compliance. Among the points which are highlighted within the program there can be anti-discrimination principle, misconduct preventive measures, employee and consumer privacy rules, as well as hiring procedure and security requirements.
Anti-bribery policy
Anti-corruption policies are strict and clear. Businesses guard their reputation emphasizing transparency and clarity of the processes.
Departments
management
assurance
Many organizations include a remark addressing third parties which are expected to follow the rules with the same willingness.
The policies are developed and governed by Legal,
Ethics & Compliance managers
Reducing insider threats
Internal threat mitigation solution helps you shape the framework and supervise the adherence to the rules, tweak the knobs of the company’s monitoring mechanism in order to adjust the level of controls and the relevance of measures taken to ensure ongoing surveillance within an organization. The system assists you with creating policies for the scope of your company and corporate culture.
Instruments helping to oversee the workflow and maintain a healthy workplace environment prevent incidents caused by violating any section of the framework.
02
Iternal
Controls
Segregation of Duties (SoD)
Conduct an analysis – determine who has access rights and what data is accessed.
Build a framework in accordance with which the roles and tasks will be assigned, and any allocation contradicting the rules or any deviation will be promptly detected. As soon as misassignment is identified it is easier to discern a problem and prevent a fraud. The concept of the least privilege dictates a play-safe but helpful approach.
Properly introduced and supervised SoD matrix helps you turn a fastidious and exacting job into an accurate software overseer.
SearchInform’s system
SearchInform’s system facilitates SoD matrix development, detection of conflict roles and helps you map controls in order to recognize them promptly.
The correct segregation of duties eliminates threats related to excessive permissions and arbitrariness.
1
Segregation of duties prevents organizational conflict caused by employees who supervise their own performance
2
One person can’t do both create and approve or prepare and assess
Conflict roles
management
assurance
Three lines of defense
1 line
Business functions, Operational management
Full responsibility for the risks, providing correct controls conforming to the highest standard
2 line
Internal Control, Risk Management, Information Security, Compliance, Financial Control
Implementation of efficient risk management program, providing relevant information about risks
3 line
Internal Audit
Audit performing, ensuring consistent application of efficient measures
Risk Assessment Matrix
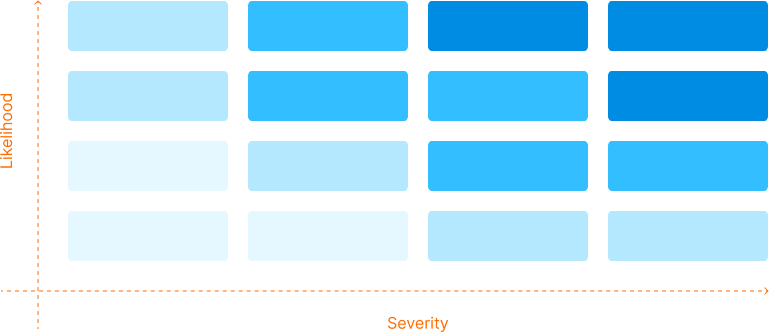
Internal Audit analyzes the performance of Internal Control. The department evaluates and verifies the ways a business understands risks and requirements.
Continuous auditing
Internal Audit instruments allow continuous auditing running in the background of your workflow. You can look at and study the red flags any time and consider launching an investigation.
Sign up for a free trial
SearchInform uses four types of cookies as described below. You can decide which categories of cookies you wish to accept to improve your experience on our website. To learn more about the cookies we use on our site, please read our Cookie Policy.
Necessary Cookies
Always active. These cookies are essential to our website working effectively.
Cookies does not collect personal information. You can disable the cookie files
record
on the Internet Settings tab in your browser.
Functional Cookies
These cookies allow SearchInform to provide enhanced functionality and personalization, such as remembering the language you choose to interact with the website.
Performance Cookies
These cookies enable SearchInform to understand what information is the most valuable to you, so we can improve our services and website.
Third-party Cookies
These cookies are created by other resources to allow our website to embed content from other websites, for example, images, ads, and text.
Please enable Functional Cookies
You have disabled the Functional Cookies.
To complete the form and get in touch with us, you need to enable Functional Cookies.
Otherwise the form cannot be sent to us.

Subscribe to our newsletter and receive a bright and useful tutorial Explaining Information Security in 4 steps!

Subscribe to our newsletter and receive case studies in comics!